
IBM i SOLUTIONS
IBM i solutions for malware and ransomware defense
Harden and integrate IBM i into enterprise-wide security systems for comprehensive protection against advance cyber threats with security solutions from Precisely
Defending against malware and ransomware
The ever-escalating threats to your business posed by ransomware and all forms of malware cannot be ignored. Cyber-criminals are employing every technology and tactic available to defeat your security systems and then go completely unnoticed as they systematically penetrate and catalog your systems and data to methodically prepare for a coordinated, carefully orchestrated, multipronged attack.
IBM has always built comprehensive advanced security capabilities into IBM i, giving the platform a sterling reputation for system security and data protection. But IBM i hardware, applications and data are increasingly integrated with other platforms, across your enterprise and across the web to partners, service providers and cloud-based e-commerce systems.
Cyber-criminals are no longer targeting individual applications or data sets. They are attacking entire interconnected business ecosystems, leveraging any tiny security gap on any member system or network to gain a foothold, after which they methodically move up, down and across every possible connection to find the most lucrative targets.
Clearly, defending against such sophisticated multi-target attacks requires equally sophisticated and integrated security planning and the deployment of leading-edge security technology to build a coordinated and multi-layered defense.


Core elements of malware and ransomware defense
In order to plan and implement effective defenses against malware and ransomware, it is important to clearly understand why these threats are different, how they work and why they are so dangerous.
Although malware threats have been around for many years, the more recent versions are becoming much more sophisticated. Just the pace at which new variations of viruses are appearing makes it a challenge to maintain security, even with modern anti-virus, threat intelligence feed and endpoint security solutions in place.
But the most important factor escalating the danger of cyber threats is the shift from using spam technology to deliver the “payload” to applying active, human operation to execute ransomware attacks. Intelligent, flexible, interactive planning and execution mean that detection and prevention cannot be packaged and delivered in advance through security software and services.
In a typical attack, security gaps or vulnerabilities are intelligently probed and assessed. Once identified, any access point or vector into your systems will be leveraged to completely avoid and negate all other protections. By learning and mimicking ‘normal’ user behaviors and exploiting any gaps in IBM i user profile authority controls to sequentially leverage and upgrade their clearance, the hacker can evade notice while quietly accessing and reconfiguring processes, opening up network pathways, and exploring your data stores.
With deep knowledge in hand and complete access established, the actual attack is then carefully planned and executed incrementally, slowly, and patiently over weeks or even months. No sudden moves, just small, seemingly normal, inconsequential changes.
When the hacker is ready, the customized, carefully orchestrated attack is executed so quickly and efficiently that it is essentially a “Zero-Minute” attack that makes Zero-Day attacks look slow and sloppy by comparison.
Because of this, the only practical approach to defending against today’s advanced malware and ransomware attacks is to establish a multi-layered defense that uses every possible security tool and tactic available. Among the methods and tools that top security experts believe are essential for companies of any size to employ are:
- Aggressive use of VPNs
- Multi-Factor Authentication (MFA)
- Zero Trust and Least Privilege Authority
- Pervasive Data Encryption / Tokenization
- Logical and Physical network segmentation and control
- Frequent, “air-gapped,” and encrypted offline DR backups
- Automated, integrated security monitoring and alerting
- Continuous security analysis and reporting
Defending against breach – external and internal points of entry
The first layer of defense against malware and ransomware involves establishing and enforcing strict security protocols that ensure effective, automated control over every point and method of access. This must include controlling access from external sources, of course, but it is just as critical to defend against “insider” threats because cyber-thieves prowling your systems have become so expert at blending in with your employees, contractors, and business partners, and even your security team.
A central feature of IBM i security is the granting and control of special or “elevated” access authority to users, on an individual basis or by assigning them to a group-specific user profile. Some roles have a valid business case for having access to data such as customer lists, source code, financial information, intellectual property, employee HR files, and other information. But too often, less than strict control over access rights results in too many overly powerful users, or temporary permissions that are never actually revoked, resulting in multiple easily exploited options for a ransomware attacker to leverage.
Compounding this problem is excessive reliance upon basic password-based authentication and single-sign on. The many weaknesses of passwords as security are legend. But at root, they are weak because they are so simple to use, and just as easy to share or lose. It only takes one errant sticky note to open up your entire organization to a devastating ransomware attack.
The IBM i platform includes extensive options for applying access controls, not just for log in but for limiting or denying access to systems and data on a very granular level. But manually establishing and maintaining effective and detailed access controls can quickly become overwhelming even for smaller organizations and does not scale easily for managing large and complex environments.
So, to enable and maintain security against breach, it is necessary to fully apply state-of-the-art security technologies such as those discussed earlier. Precisely can help you establish effective perimeter defenses against malware and ransomware with our Assure Security solutions for IBM i.
Assure Multi-Factor Authentication strengthens logon security for configured users. Certified for RSA SecurID, Assure Multi-Factor Authentication also supports RADIUS servers or a Precisely provided authenticator.
Assure Elevated Authority Manager automatically controls and manages the grant higher levels of user authority on an as-needed and time-limited basis, while comprehensively monitoring the actions of elevated profiles. Flexible, highly customizable rules define the context in which authority can be granted and the method to be used for elevating authority.
Assure System Access Manager enables tight, automated control of all entry points and pathways into IBM i systems, including network protocols, communications ports, database protocols, and command lines. Granular rules control access based on user profile settings, date and time, IP address and more.


Monitoring for signs of compromised security
Effective multi-level security defense can only be achieved if, for each layer and method of security implemented, the assumption is made that it will eventually be defeated. This means a mindset that repeatedly asks what happens next, not if but when any given layer of defense fails. In the case of advanced ransomware threats, it must be assumed that cyber thieves will get in. At that point, your security strategy must shift from preventing breach to detecting it.
Because of the advanced human-operated, intelligent user-spoofing tools and methods employed by cyber-crooks, this is no simple matter. It becomes an almost fuzzy-logic process to surveil systems and identify seemingly normal events that, considered in isolation, may not be enough to warrant investigation but which may in fact indicate an attack may already be in progress.
This is especially difficult when the attacker is careful to make only tiny, incremental moves or changes and to limit total activity to short, non-obvious frequency or elapsed time. This “burrowing” phase, during which the attacker remains quiet most of the time, can go on for days and weeks, or even months while elevated privileges are acquired and additional accounts, systems and data sets are compromised.
Defending against malware and ransomware in this phase requires deep, granular and automated monitoring along with a comprehensive, enterprise-wide view to analysis, alerting and reporting. A very small yet odd event on your IBM i platform, such as downloading just a few records under a privileged vendor’s profile, can indicate big trouble for your entire enterprise if, in fact, that vendor is no longer active in your payables systems or has not logged in for several months. Only through truly automated and integrated, cross-platform security monitoring and analysis can such tenuous logical connections become an actionable indicator of compromise (IOC).
Precisely offers powerful Assure Security solutions to help you establish and automate deep, continuous visibility into security issues and generate clear, actionable alerts and reports on IBM i system activity, database changes and views of Db2 data.
Assure Monitoring and Reporting seamlessly extracts insights from IBM i journal data and delivers alerts and reports on security incidents and compliance deviations. Seamlessly integrate the full range of advanced IBM i security capabilities into your enterprise SIEM solution complete, fully coordinated, security.
Assure Db2 Data Monitor controls and monitors views of highly confidential Db2 data, ensuring the security of your most valuable corporate data while meeting the most stringent regulatory requirements for data confidentiality.
Hardening the ultimate targets – data at rest and in motion
With rare exception, the primary motivator for cyber-criminals is financial gain. And they understand that your data is your most precious asset. So, all their techno-trickery is ultimately directed at finding and “kidnapping” your data via encrypting it.
Experts talk about ‘remediation’ after a breach, focusing on recovering data and repairing systems. But after a fully successful ransomware attack, with your data locked up by unbreakable encryption, remediation is incredibly difficult, time consuming and very, very expensive. In some cases, it may be completely impossible.
To help ensure that the situation never gets to that point, it is critically important to make your data a “hard target” both by making it much harder to find and rendering it essentially worthless to hackers by encrypting it before they can get to it.
This fundamental requirement applies to all your data, wherever it exists, and at all times. It applies while data is being viewed, created, or modified in a production system; while it is being used in development testing; or as it is being sent and received across internal or external network connections.
And, for complete defense against malware and ransomware attacks, all HA and DR backup data must also be encrypted and maintained in storage systems which are beyond the reach of cyber-criminals.
Precisely’s advanced, state-of-the-art encryption, tokenization, and masking technologies for IBM i enable comprehensive, effective data privacy and security protection.
Assure Encryption defends data at-rest using the only NIST-certified AES encryption for IBM i. It fully supports FIPS 140-2 compliant Alliance Key Manager from Townsend Security as well as for many leading OASIS KMIP-compliant key managers. Assure Encryption also offers built-in masking, tokenization and user profile-based data access control.
Assure Secure File Transfer shields data moving across networks. Files are encrypted for transfer using globally recognized standard protocols including Secure Shell (SSH SFTP) and Secure FTP (SSL FTPS). Optional PGP encryption further protects data both at the source and destination.
Backing up and fully securing all your data is a critical and essential component of your overall defense against malware and ransomware. Assure MIMIX solutions offer different levels of HA and DR data protection fitted to the needs of any size organization.

Integrating and coordinating security systems and processes
Ultimately, the strongest and most effective security is only achieved through rigorous contingency planning and the coordination of multiple security elements to surround the target with multiple layers of defense.
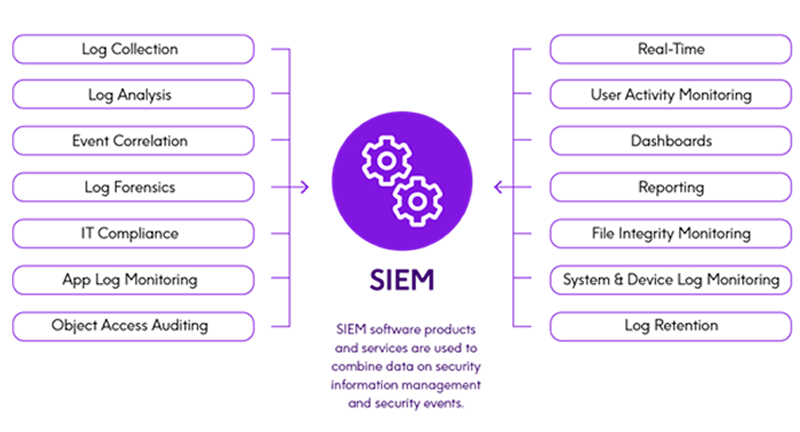
Security Information and Event Management (SIEM) solutions are integral to security strategies for many organizations today. Because IBM i is deeply integrated operationally with all your other systems and platforms, it is critical that IBM i security is also fully integrated into your overall security plans and systems.
Due to the wide range of security log sources which need to be integrated, as well as the proprietary nature of its data formats, integrating IBM i security information into an enterprise SIEM platform through in-house development and maintenance is challenging and time consuming, requiring specialized, platform-specific skills.
The key is to implement a third-party solution to automate the monitoring and presentation of IBM i security log data to your SIEM solution.
Assure security solutions are designed to fully and seamlessly integrate IBM i security into SIEMs such as IBM QRadar, Solar Winds, Splunk, ArcSight, LogRhythm, LogPoint, Netwrix, and others, for analysis alongside security data from other platforms.
Read IBM i Compliance and Security: Identifying the Events That Matter Most to learn more about integrating IBM i systems into your SIEM solution.



