
Ensure the Security and Availability of IBM i and AIX Systems
Protect IBM i systems with layered security controls and ensure IBM i and AIX availability through automated high availability, ransomware defense, and audit-ready controls to reduce risk and ensure continuous operations.
Secure and resilient IBM i and AIX operations
Built for continuous availability, audit readiness, and cyber resilience
This solution secures IBM i systems through layered, purpose-built controls and ensures the availability of IBM i and AIX systems for organizations running mission-critical workloads. Designed for IT and infrastructure leaders in regulated and always-on environments, it combines real-time high availability across IBM i and AIX with purpose-built IBM i security controls to reduce downtime, defend against ransomware, and simplify compliance. With seamless integration and no disruption to business processes, organizations gain confidence that their Power Systems environments remain secure, resilient, and continuously available.
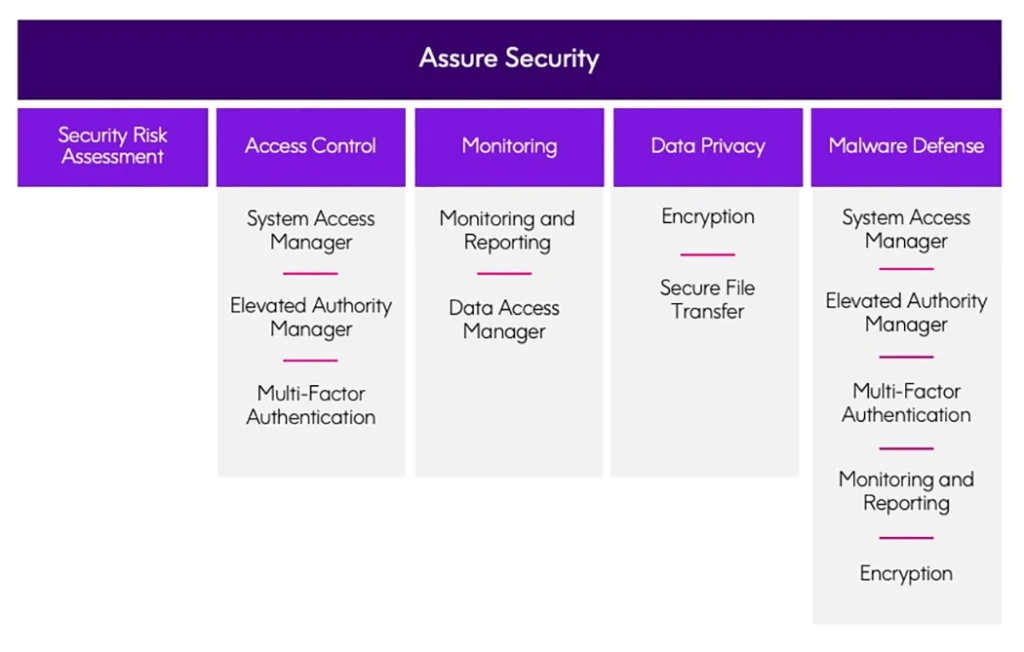
Comprehensive IBM i protection with Assure Security


“The biggest benefit of Assure MIMIX HA is that if there is a problem, we can be up and running again within five minutes.”
George Gallant, System Manager
The All England Lawn Tennis Club
How Precisely protects IBM i and AIX systems
Ensure continuous availability
Automate real-time replication and failover for IBM i and AIX environments to minimize downtime during planned maintenance, outages, or unexpected disruptions—keeping critical systems running.

Strengthen IBM i security
Protect IBM i systems with granular access controls, continuous monitoring, and automated audit reporting to defend against ransomware, insider threats, and compliance gaps.
Simplify audits and compliance
Generate audit-ready reports in minutes, enforce security policies consistently, and demonstrate compliance with regulations like PCI-DSS, SOX, and J-SOX without manual effort.

Maintain always-on IBM i and AIX operations
High availability without disruption
Organizations running 24×7 IBM i and AIX workloads rely on continuous system availability to protect revenue and customer trust. This solution ensures near-zero downtime through real-time replication and automated role swaps, allowing teams to perform upgrades, maintenance, and disaster recovery testing across IBM i and AIX environments without interrupting critical business processes.
Defend against ransomware and cyber threats
Purpose-built security for IBM i
IBM i systems are increasingly targeted by sophisticated attacks. With continuous monitoring, exit-point security, and automated access controls, organizations can detect threats early, prevent unauthorized activity, and reduce the impact of ransomware or insider misuse—while maintaining system performance.


Streamline audits and compliance reporting
Audit-ready by design
Manual audit preparation drains time and resources. This solution automates security reporting and compliance workflows, enabling organizations to meet regulatory requirements faster, reduce audit risk, and maintain continuous visibility into IBM i security posture.

Free IBM i Security Risk Assessment
Get a clear view of your IBM i security posture. This free assessment identifies vulnerabilities, access risks, and compliance gaps—helping you prioritize actions and strengthen defenses.
Take the next step with confidence
Want to secure your IBM i and ensure availability across IBM i and AIX? Let’s get started!
Fill out the form and one of our experts will be in touch.
Frequently asked questions
Does this solution support both IBM i and AIX?
High availability is supported for both IBM i and AIX using Assure MIMIX. Assure Security supports IBM i.
Can we maintain availability during upgrades and maintenance?
Yes. Real-time replication and automated role swaps allow upgrades, patches, and maintenance to occur with minimal or no downtime.
How quickly can we recover from an outage?
Most customers are able to recover systems and resume operations within minutes, depending on environment size and configuration.
Does this help with compliance audits?
Yes. Automated reporting and continuous monitoring simplify audits for regulations such as PCI-DSS, SOX, and J-SOX.
Is there a way to assess our current IBM i security risk?
Yes. You can start with a free IBM i Security Risk Assessment to identify risks and recommended next steps.





